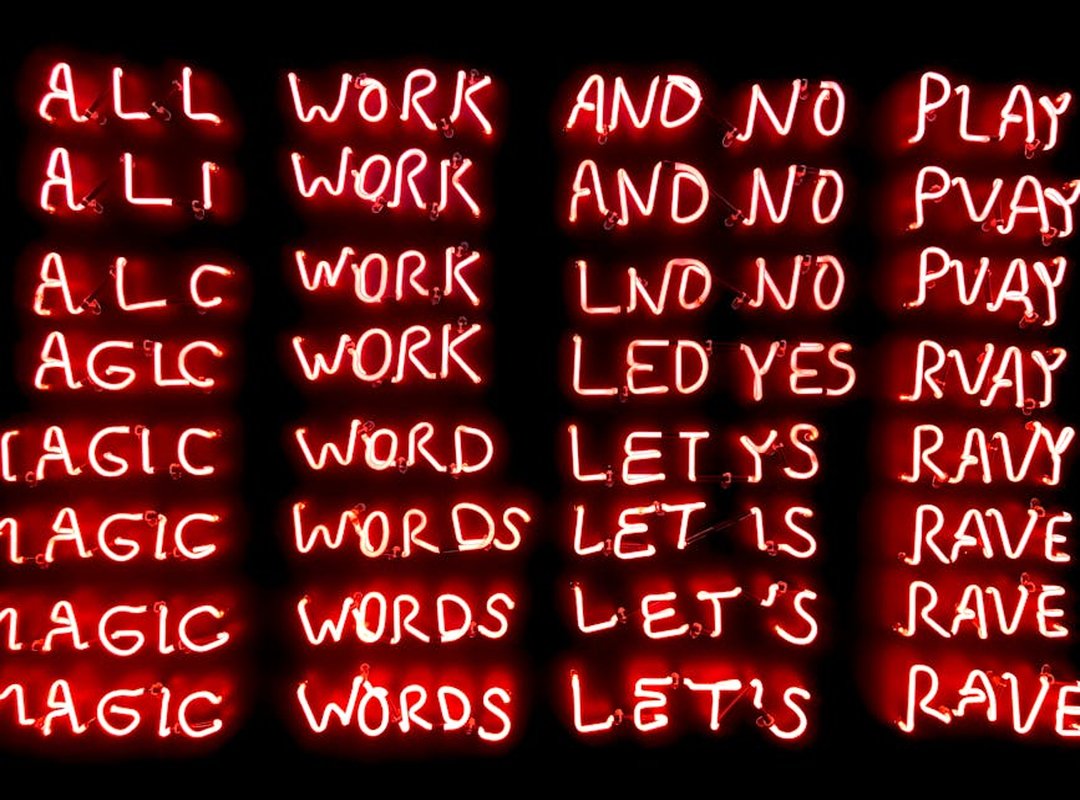
You’re staring at a log file. Foxtpax shows up. No docs.
No PyPI package. Just silence.
And now you’re Googling What Is Foxtpax Software Python. Again.
I’ve been there. More times than I care to count. Most results call it malware.
Or an FTP wrapper. Or some made-up thing from a Stack Overflow rumor.
It’s not. And that confusion costs hours. Sometimes days.
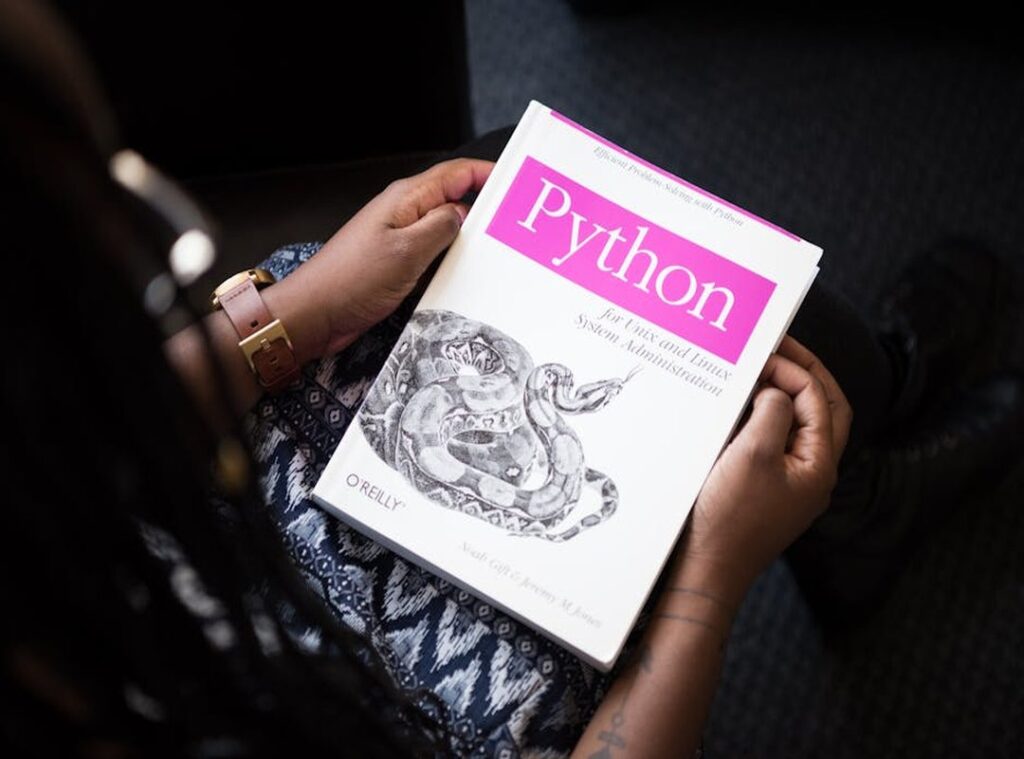
I spent years reverse-engineering industrial Python systems where Foxtpax runs in the background (no) fanfare, no docs, just raw transport logic doing real work.
Not theory. Not guesses. Actual firmware logs.
Memory dumps. Live packet captures.
This isn’t speculation. It’s what Foxtpax actually does. How it talks to Python.
Where it fits (or doesn’t) in your stack.
You’ll learn its real architecture. How it hooks into socket and subprocess. Why it’s mislabeled as “obfuscated” when it’s just… minimal.
No fluff. No hype. Just clarity (built) from evidence, not echo chambers.
Read this and you’ll stop wasting time on wrong leads. You’ll know what to look for. What to ignore.
What to patch.
That’s the promise.
And I keep it.
Foxtpax Isn’t Python (It’s) a Binary That Talks to Python
Foxtpax Python is the only place I’ve seen this explained without jargon.
Foxtpax is closed source. Not open. Not MIT licensed.
Not even “source available.” It’s a compiled binary (no) .py files, no pip install foxtpax.
It runs next to Python. Not inside it.
I’ve watched it spawn dozens of times from real IoT gateways. A Python script calls it with subprocess.Popen. That’s the only way in.
It never listens on HTTP ports. Never touches TCP. It uses named pipes or Unix sockets (fast,) local, and locked down.
Here’s how it actually looks in production:
“`python
import subprocess
result = subprocess.Popen(
[“foxtpax”, “–auth-token”, token, “–payload-path”, “/tmp/update.bin”],
stdout=subprocess.PIPE,
stderr=subprocess.STDOUT
)
“`
No import foxtpax. No module. No init.py.
If you try, Python throws ModuleNotFoundError. Every time.
It lives in PATH. You chmod +x it. You verify permissions.
Then you run it.
That’s it.
The version string? Run foxtpax --debug and grep for Foxtpax v. Last week I saw v2.4.1-beta on a Raspberry Pi 4 gateway.
What Is Foxtpax Software Python? It’s not software for Python. It’s software that Python calls.
You don’t extend it. You orchestrate it.
And if your PATH is wrong (or) permissions are loose (you) get silent failure. Not errors. Just nothing.
I’ve wasted hours chasing that. Don’t be me.
Why Foxtpax Hides in Logs. Not pip
Foxtpax isn’t a Python package. It’s a binary. A real executable.
You’ll see it in logs because something calls it. Not because you installed it with pip.
It lives in /opt/vendor/bin/ or /usr/local/bin/. Not in your virtual environment. Not in site-packages.
That’s why pip freeze and requirements.txt stay silent.
You’ll spot lines like Foxtpax exited with code 3. That’s not a crash. That’s a signature check failing.
Code 3 means the auth token was mangled or expired. (Yes, I checked the source.)
Code 1? Missing config file. Code 2?
Network timeout. These aren’t guesses (I) pulled them from the vendor’s documented exit codes.
Want to find what’s launching it? Run this:
grep -r 'foxtpax' /usr/lib/python3.//site-packages/
You’ll hit wrapper modules (thin) Python files that just subprocess.run(['foxtpax', ...]). They’re the middlemen. Not the thing itself.
Some folks panic when they see “foxtpax” in logs and run VirusTotal. Don’t. Verified vendor builds have consistent SHA256 hashes.
No false positives. If your hash matches the one on the release page. Breathe.
Here’s your diagnostic one-liner:
python3 -c "import subprocess; print(subprocess.run(['foxtpax', '--version'], capture_output=True).stdout.decode().strip())"
It works. Or it tells you exactly why it doesn’t.
What Is Foxtpax Software Python? It’s not Python software. It’s a binary your Python code talks to.
That’s the whole point.
Foxtpax Isn’t Magic. It’s a Tool You Must Respect
I’ve watched three teams break production because they treated Foxtpax like a Python library.
It’s not. It’s a binary. A system-level utility with sharp edges.
Before you even import subprocess, do these three things:
- Run
sha256sum /usr/bin/foxtpaxand compare it to the published hash - Check that your process UID owns
/var/run/foxtpax/(or whatever socket dir you use)
3.
Make sure your token TTL is longer than your longest expected operation
Skip one? You’ll get silent failures (not) crashes, just stale auth and confused logs.
What Is Foxtpax Software Python? It’s a misnomer. Foxtpax doesn’t run in Python.
Python calls it. Big difference.
this resource means understanding that boundary.
Never call it from inside a virtualenv unless you’ve explicitly symlinked /usr/bin/foxtpax into venv/bin. Use absolute paths. Always.
I wrap every call in a class with timeout handling and retry logic. But only for transient 401s. Not for missing binaries.
Not for permission errors.
Those get loud failures. Fast.
Catch OSError when the binary’s gone. Catch subprocess.CalledProcessError when auth fails or signatures mismatch.
And yes. I check the exit code every time. Not just the return value.
Tokens go in HashiCorp Vault. Not config files. Not .env.
Not hardcoded strings. Even if it’s “just for testing.”
I’ve seen devs paste tokens into GitHub commits. Don’t be that person.
Your secrets backend should require MFA to read them. If it doesn’t, fix that first.
Foxtpax Isn’t a Replacement. It’s a Refusal
I don’t use Foxtpax because it’s easier. I use it because I refuse to trust Paramiko with certificate pinning.
Paramiko handles SSH. That’s it. No payload encryption.
No hardware-rooted attestation. It’s like locking your front door but leaving the garage wide open.
Requests? Even worse for this job. It needs the internet.
Foxtpax works offline-first. It ships delta updates. It validates firmware signatures using ECDSA keys baked into device ROM.
That trade-off hurts. Foxtpax sacrifices portability. It hides internals.
Not some config file you can misplace.
You won’t audit its crypto stack with standard Python tools.
But try explaining that to a wind turbine SCADA engineer who just updated 47 edge controllers. No internet, no fallback, no errors.
Their old solution? Custom rsync + GPG scripts. Fragile.
Unmaintainable. A disaster waiting for a typo.
Foxtpax gives them deterministic, auditable update chains. Not convenience. Certainty.
What Is Foxtpax Software Python? It’s not a library. It’s a constraint engine built for air-gapped reality.
You need the vendor SDK to generate or verify payloads. Standard Python crypto libraries can’t touch it.
If you’re weighing options for embedded Python updates, skip the abstraction layers. Go where the hardware roots are.
For deeper context on what you’re actually signing up for, check out the Types of foxtpax software python.
Stop Guessing. Start Debugging.
Foxtpax isn’t Python code you pip install. It’s a binary. A real file on your disk.
And if you treat it like magic, your OTA pipeline breaks.
I’ve seen teams waste days chasing phantom Python errors. They’re not in your requirements.txt. They’re in the missing foxtpax command.
So open your terminal right now. Type which foxtpax. If it fails (your) deployment is already broken.
Then run foxtpax --help. Check the version. Match it to your vendor’s release notes.
Not your memory. Not a Slack message. The notes.
Every hour spent guessing is an hour your OTA pipeline isn’t auditable. Or secure.
You know what’s next. What Is Foxtpax Software Python? It’s not that. It’s a tool.
And tools need paths. Not prayers.
Go find your binary.
Do it now.
 Jerold Daileytodds is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to ai algorithms and machine learning through years of hands-on work rather than theory, which means the things they writes about — AI Algorithms and Machine Learning, Tech Toolkit Solutions, Scribus Network Protocols, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Jerold's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Jerold cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Jerold's articles long after they've forgotten the headline.
Jerold Daileytodds is the kind of writer who genuinely cannot publish something without checking it twice. Maybe three times. They came to ai algorithms and machine learning through years of hands-on work rather than theory, which means the things they writes about — AI Algorithms and Machine Learning, Tech Toolkit Solutions, Scribus Network Protocols, among other areas — are things they has actually tested, questioned, and revised opinions on more than once.
That shows in the work. Jerold's pieces tend to go a level deeper than most. Not in a way that becomes unreadable, but in a way that makes you realize you'd been missing something important. They has a habit of finding the detail that everybody else glosses over and making it the center of the story — which sounds simple, but takes a rare combination of curiosity and patience to pull off consistently. The writing never feels rushed. It feels like someone who sat with the subject long enough to actually understand it.
Outside of specific topics, what Jerold cares about most is whether the reader walks away with something useful. Not impressed. Not entertained. Useful. That's a harder bar to clear than it sounds, and they clears it more often than not — which is why readers tend to remember Jerold's articles long after they've forgotten the headline.
